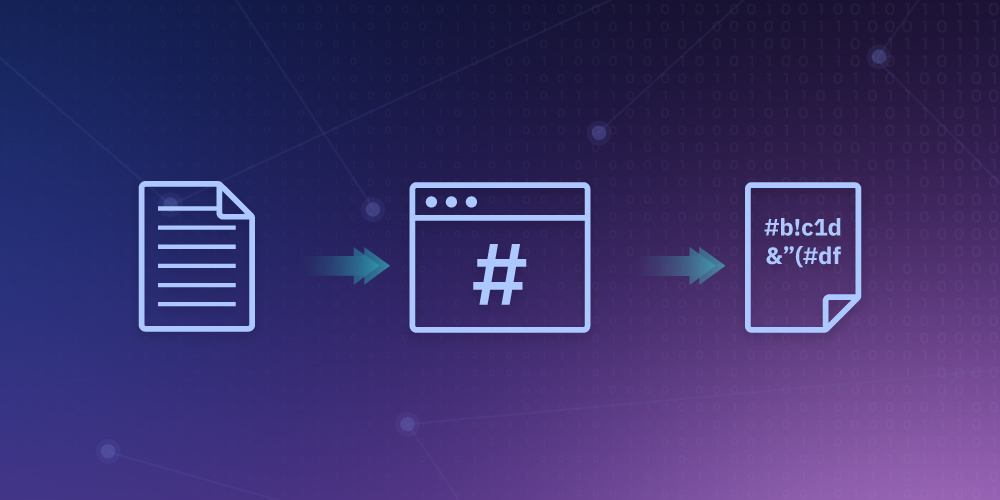
Hashing is an indispensable and ubiquitous tool used for a variety of tasks, including authentication, data integrity checking, file protection, and even malware detection. Many hashing algorithms differ in cryptographic strength, complexity, bit depth, and other properties. It is believed that the idea of hashing belongs to an IBM employee, appeared about 50 years ago, and has not changed fundamentally since then. But nowadays hashing has acquired a lot of new properties and is used in many areas of information technology.
Hashing means entering information of any length and size in the original string and returning the result of a fixed-length given by the hashing function algorithm. In the context of cryptocurrencies such as Bitcoin, transactions after hashing at the output look like a set of characters of a certain length algorithm (Bitcoin uses SHA-256).
Hash function
It is a specific kind of hash that is secure and ideal for cryptography. Hash functions have the following features:
- Determinism - for a certain input value, a fixed amount of hashes must be produced each time.
- Computational efficiency - the computing power must be sufficient to return the hashes quickly. Most computers can process a hash function in a split second.
- Resilience to preimage - the hash function should not provide any information about the input value.
- Collision resistant - getting two inputs that could give two outputs. Must be very difficult or impossible. Since the input value can be any length, its variations are endless.
Outputs have a fixed length and in this case, the number of options is limited. However, multiple inputs can produce the same output.
If the collision resistance is not high enough, the so-called birthday paradox can occur. This is an attack in which mathematics prevails over probability theory. If we apply this theory to hashing, it becomes clear that technically no hash function is completely collision-resistant, but it can take a very long time before that happens.
Bitcoin hash function
Bitcoin operates on the blockchain and uses the SHA-256 hashing algorithm (256 cryptographic hashing algorithms). With its help, any amount of information can be converted into a string of 64 characters. Bitcoin hash functions serve three main purposes:
- Mining - miners compete to solve problems. Each miner takes information from blocks they already know about and builds a new block out of them. If the algorithm outputs a value less than the target digit, it is considered valid and can be accepted by the rest of the network participants. Thus, the miner gets the right to create the next block.
- Connecting blocks - for added security. Each block in the blockchain is linked to the previous one, which is achieved through a hash pointer (variables storing the address of another variable). Essentially, each block contains the hash result from the previous block in the blockchain. Thanks to this feature, you can easily track the history in the blockchain and eliminate the possibility of adding a malicious block to the network.
- Key generation - private and public keys are required to send or receive cryptocurrency. Both keys are linked to each other via a hash function. It is an integral component that is excluded
Hash rate
Hash rate means how fast these hashing operations take place during mining. A high hash rate means that more people and miners are involved in the mining process, and as a result, the system is functioning normally. If the hash rate is too fast, the difficulty level increases proportionally. If the hash speed is too slow, then the difficulty level decreases accordingly.
Closing line
The hash function provides the cryptocurrency with a high level of security and versatility. Even though there is no completely 100% protection against hacking, this approach provides the highest level of security available today.
With hash functions, you can hash passwords and encrypt other data, protecting against falsification during transmission. In other words, you can make sure that the file has not undergone any changes along the way somewhere by comparing its hashes taken immediately before sending and immediately after receiving. If the data has changed even by only 1 byte, the hash codes will differ.
Cryptographic hash functions are vital for almost all cryptocurrency networks, so understanding their properties and how they work is important in the process of interaction.